Biztonsági szemle

2024. január 2.
Biztonsági szemle
Operations at Massachusetts hospital hit by cyberattack
Massachusetts-based Anne Jaques Hospital of the Beth Israel-Lahey Health System had its emergency services and electronic health records systems disrupted by a cyberattack that reportedly commenced on Christmas Eve, reports The Record, a news site by...

2024. január 2.
Biztonsági szemle
Windows defenses evaded by new DLL search order takeover
Windows defenses evaded by new DLL search order takeover Windows 10 and Windows 11 systems could have their security defenses evaded to facilitate malicious code execution through a new dynamic link library search order hijacking technique, according...

2024. január 2.
Biztonsági szemle
Google OAuth endpoint exploited by various malware
BleepingComputer reports that expired authentication cookies are being revived for account access by numerous information-stealing malware strains by leveraging the newly discovered MultiLogin Google OAuth endpoint.

2024. január 2.
Biztonsági szemle
Novel JinxLoader malware loader emerges
Phishing attacks using the novel JinxLoader malware loader have been launched to facilitate the deployment of the Formbook and XLoader payloads, reports The Hacker News.

2024. január 2.
Biztonsági szemle
Israeli orgs subjected to suspected Iranian hacking attacks
Suspected Iranian state-backed hacking group Cyber Toufan has taken credit for compromising dozens of organizations across Israel in late November amid the ongoing Israel-Hamas war, according to The Record, a news site by cybersecurity firm Recorded...
2024. január 2.
Biztonsági szemle
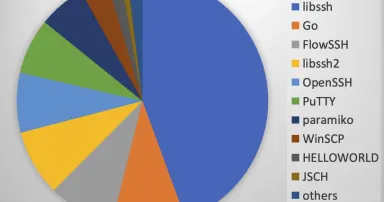
Fingerprinting SSH Identification Strings, (Tue, Jan 2nd)
For HTTP, logging and fingerprinting browser user agents is standard practice. Many anti-automation tricks use the user agent and compare it to other browser artifacts, for example, supported JavaScript APIs, to detect bots. SSH offers an...

2024. január 2.
Biztonsági szemle
Israel Battles Spike in Wartime Hacktivist, OT Cyberattacks
Israel's cybersecurity industry made strides in the past year despite the backdrop of the war in Gaza.
2024. január 2.
Biztonsági szemle
CISO Planning for 2024 May Struggle When It Comes to AI
Artificial intelligence (AI) is constantly evolving. How can security executives plan for something so unpredictable?

2024. január 2.
Biztonsági szemle
Localization Mandates, AI Regs to Pose Major Data Challenges in 2024
With more than three-quarters of countries adopting some form of data localization and, soon, three-quarters of people worldwide protected by privacy rules, companies need to take care.

2024. január 2.
Biztonsági szemle
Attackers Abuse Google OAuth Endpoint to Hijack User Sessions
Infostealers such as Lumma and Rhadamanthys have integrated the generation of persistent Google cookies through token manipulation.
2024. január 2.
Biztonsági szemle
Startups Scramble to Build Immediate AI Security
AI may be inherently insecure, but only a handful of startups have put forward real visions to mitigate AI's threats and keep data private.
2024. január 2.
Biztonsági szemle
Biggest AI trends of 2024: According to top security experts
Cybersecurity prognosticators share predictions for artificial intelligence's uses, abuses and surprising impact on businesses risks in the year ahead.
Oldalszámozás
- Előző oldal ‹‹
- 1150. oldal
- Következő oldal ››