Security Bulletin

18 Oct 2023
Biztonsági szemle
North Korea's Kimsuky Doubles Down on Remote Desktop Control
The sophisticated APT employs various tactics to abuse Windows and other built-in protocols with both custom and public malware to take over victim systems.

18 Oct 2023
Biztonsági szemle
Government-backed actors exploiting WinRAR vulnerability
Google's Threat Analysis Group analyzes recent state-sponsored campaigns exploiting the WinRAR vulnerability, CVE-2023-38831.

18 Oct 2023
Biztonsági szemle
FBI boss slams 'unprecedented' Chinese cyberespionage and IP theft
Christopher Wray and other Western intelligence agency leaders used a public forum in California to present a united front against China’s industrial spying.

18 Oct 2023
Biztonsági szemle
The Need for a Cybersecurity-Centric Business Culture
Building a culture of cybersecurity is achievable by acknowledging its importance and consistently reinforcing that message.

18 Oct 2023
Biztonsági szemle
Pro-Iranian Hacktivists Set Sights on Israeli Industrial Control Systems
The hacktivists known as SiegedSec identify ICS targets, but there's no evidence of attacks yet.
18 Oct 2023
Biztonsági szemle
Israeli Cybersecurity Startups: Impact of a Growing Conflict
For Israeli startups and those closely linked to the country, the deepening crisis in the Middle East following the deadly Hamas attacks of Oct. 7 pose a fraught mix of complications.

18 Oct 2023
Biztonsági szemle
Data Security and Collaboration in the Modern Enterprise
The "CISO Survival Guide" explores the complex and shifting challenges, perceptions, and innovations that will shape how organizations securely expand in the future.
18 Oct 2023
Biztonsági szemle
Jupyter Notebook Ripe for Cloud Credential Theft, Researchers Warn
If not correctly locked down, Jupyter Notebook offers a novel initial access vector that hackers can use to compromise enterprise cloud environments, as seen in a recent hacking incident.
18 Oct 2023
Biztonsági szemle
Middle East Crisis: Understanding the potential threats – and how the cybersecurity industry can take action
As President Biden gets set to visit Israel in the midst of the Middle East Crisis, organizations must start by understanding that cyber warfare knows no borders, then band together as a world community to counteract the threats.
18 Oct 2023
Biztonsági szemle
Reverse Engineering BMCs and Other Firmware - Vladyslav Babkin - BTS #15

17 Oct 2023
Biztonsági szemle
Amazon Quietly Wades Into the Passkey Waters
The move by the e-commerce kahuna to offer advanced authentication to its 300+ million users has the potential to move the needle on the technology's adoption, security experts say.
17 Oct 2023
Biztonsági szemle
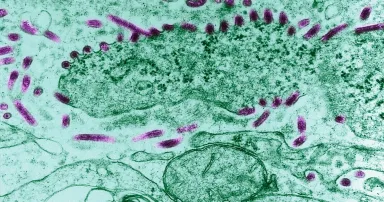
Chatbot Offers Roadmap for How to Conduct a Bio Weapons Attack
Once ethics guardrails are breached, generative AI and LLMs could become nearly unlimited in its capacity to enable evil acts, researchers warn.
Pagination
- Previous page ‹‹
- Page 910
- Next page ››