Security Bulletin

18 May 2026
Biztonsági szemle
TeamPCP Supply Chain Campaign: Activity Through 2026-05-17, (Mon, May 18th)
Since the last update, the TeamPCP supply chain campaign produced its loudest stretch since the March Trivy disclosure: an officially confirmed Checkmarx Jenkins plugin compromise and a new self-spreading Mini Shai-Hulud worm across npm and PyPI.

18 May 2026
Biztonsági szemle
Shai-Hulud Worm Clones Spread After Code Release
The release of Shai-Hulud source code spells trouble for software developers as researchers worry the self-replicating worm could scale.

18 May 2026
Biztonsági szemle
Innovating at the Speed of Business: Announcing the Customer Achievement Awards AMER 2026 Finalists
We are honored to celebrate these remarkable achievements and the trust our customers place in Cisco as their technology partner.

18 May 2026
Biztonsági szemle
Fuel Tank Breaches Expand Scope of Iran's Cyber Offensive
Security experts have long warned that insecure automatic tank gauge (ATG) systems exposed on the Internet can be tampered with by threat actors.

18 May 2026
Biztonsági szemle
The Boring Stuff is Dangerous Now
AI agents capable of discovering and exploiting obscure vulnerabilities are emerging alongside developers producing vast amounts of potentially flawed AI-generated code, forcing defenders to adapt accordingly.

18 May 2026
Biztonsági szemle
Boulevard of Broken Dreams: 2 Decades of Cyber Fails
From the MGM and Caesars fiasco and MOVEit's patch nightmare to epic business blunders and the jaded reality of living in a post-breach world, Dark Reading looks back at the mistakes, miscalculations, systemic failures, and cringeworthy moments that...

18 May 2026
Biztonsági szemle
Can Laws Stop Deepfakes? South Korea Aims to Find Out
South Korea's local elections next month will be a test bed for how effective regulations might be to stymie the flow of deepfakes.

15 May 2026
Biztonsági szemle
Future of Sports Analytics: Building Trust and Intelligence with SūmerSports and Cisco
Cisco and SūmerSports demonstrate how on-premise AI infrastructure gives sports organizations the security and trust they need to turn proprietary data into a real competitive edge.

15 May 2026
Biztonsági szemle
Cyber Pioneers Ponder Past as Prologue
Robert "RSnake" Hansen, Katie Moussouris, Rich Mogull, Richard Stiennon, and Bruce Schneier reflect on how their favorite columns penned for Dark Reading over the past 20 years have stood the test of time.

15 May 2026
Biztonsági szemle
Sajtószemle – 2026. 20. hét
Megjelent a 2026. 20. hetére vonatkozó hírválogatás, amely az NBSZ NKI által 2026.05.08. és 2026.05.14. között kezelt incidensek, valamint az elosztott kormányzati IT biztonsági csapdarendszerből (GovProbe1) származó adatok statisztikai eloszlását is...
15 May 2026
Biztonsági szemle
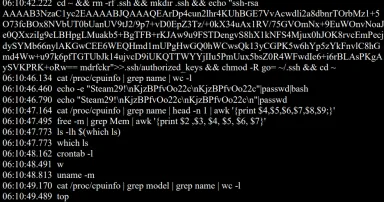
[Guest Diary] New Malware Libraries means New Signatures, (Fri, May 15th)

 
 :root {
 --isc-maroon: #7a1f1f;
 --isc-maroon-dark: #5e1717;
 --isc-link: #0066cc;
 --isc-text: #1a1a1a;
 --isc-muted: #555;
 --isc-rule: #d0d0d0;
 --isc-code-bg: #f4f4f4;
 --isc-code-text: #c0392b;&...

15 May 2026
Biztonsági szemle
ISC Stormcast For Friday, May 15th, 2026 https://isc.sans.edu/podcastdetail/9934, (Fri, May 15th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
Pagination
- Page 1
- Next page ››