Security Bulletin

29 Sep 2025
Biztonsági szemle
Ukrainian Cops Spoofed in Fileless Phishing Attacks on Kyiv
Attackers impersonate the National Police of Ukraine to deploy Amatera Stealer and PureMiner, using malicious Scalable Vector Graphics to trick victims.

29 Sep 2025
Biztonsági szemle
Kistler Improves Traffic Safety and Extends Pavement Life with Cisco Industrial Switches
Kistler Group’s KiTraffic Digital, powered by Cisco industrial switches, identifies overloaded trucks as they move at highway speeds.

29 Sep 2025
Biztonsági szemle
Lessons from an AI-Assisted Content Migration
Discussion of AI is all around us, but in my experience, practical guidance rooted in specific use cases is surprisingly rare. After spending months deep in the weeds of a massive documentation migration with AI as my assistant, I’ve learned some...

29 Sep 2025
Biztonsági szemle
Experience the Power of Connection and AI at Cisco Connect Cancun
Cisco Connect returns to the Moon Palace Hotel and Convention Center in sunny Cancun today! Even after two decades and 20 global Cisco Live events, I’m still energized by the chance to meet new faces, reconnect with friends, and experience the latest...

29 Sep 2025
Biztonsági szemle
ISC Stormcast For Monday, September 29th, 2025 https://isc.sans.edu/podcastdetail/9632, (Mon, Sep 29th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
27 Sep 2025
Biztonsági szemle
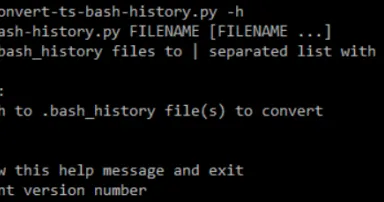
New tool: convert-ts-bash-history.py, (Fri, Sep 26th)
In SANS FOR577[1], we talk about timelines on day 5, both filesystem and super-timelines. but sometimes, I want something quick and dirty and rather than fire up plaso, just to create a timeline of .bash_history data, it...

26 Sep 2025
Biztonsági szemle
Volvo Employee SSNs Stolen in Supplier Ransomware Attack
Three international vehicle manufacturers have fallen to supply chain cyberattacks in the past month alone.

26 Sep 2025
Biztonsági szemle
From Query to Action with MCP Servers
See how Model Context Protocol (MCP) servers turn queries into real actions. This post and video reveal patterns for quicker, safer operations—giving you practical tips to streamline your workflow.

26 Sep 2025
Biztonsági szemle
Iranian State Hackers Use SSL.com Certificates to Sign Malware
Security researchers say multiple threat groups, including Iran's Charming Kitten APT offshoot Subtle Snail, are deploying malware with code-signing certificates from the Houston-based company.

26 Sep 2025
Biztonsági szemle
Prep is Underway, But 2026 FIFA World Cup Poses Significant Cyber Challenges
The world's most-popular sports contest starts in June 2026 across 16 venues in three countries: Securing the event infrastructure from cyber threats will require massive collaboration.

26 Sep 2025
Biztonsági szemle
Sajtószemle – 2025. 39. hét
Megjelent a 2025. 39. hetére vonatkozó hírválogatás, amely az NBSZ NKI által 2025.09.19. és 2025.09.25. között kezelt incidensek, valamint az elosztott kormányzati IT biztonsági csapdarendszerből (GovProbe1) származó adatok statisztikai eloszlását is...

26 Sep 2025
Biztonsági szemle
ISC Stormcast For Friday, September 26th, 2025 https://isc.sans.edu/podcastdetail/9630, (Fri, Sep 26th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
Pagination
- Previous page ‹‹
- Page 136
- Next page ››