Security Bulletin
22 Jul 2025
Biztonsági szemle
Using Generative AI for Technical Writing at Cisco ThousandEyes
Discover how CirCUIT, Cisco's internal AI Assistant, empowers the work of a technical writer.

22 Jul 2025
Biztonsági szemle
China-Backed APT41 Cyberattack Surfaces in Africa
Up to now, the prolific China-sponsored cyber-espionage group has been mostly absent from the region, but a sophisticated and highly targeted attack on an African IT company shows Beijing is branching out.
22 Jul 2025
Biztonsági szemle
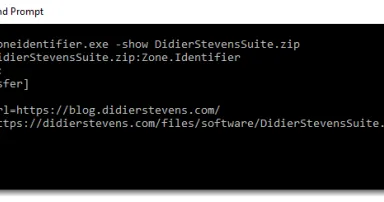
WinRAR MoTW Propagation Privacy, (Tue, Jul 22nd)
Since WinRAR 7.10, not all Mark-of-The-Web data (stored in the Zone.Identifier Alternate Data Stream) is propagated when you extract a file from an archive.

22 Jul 2025
Biztonsági szemle
Wireshark 4.4.8 Released, (Tue, Jul 22nd)
Wireshark release 4.4.8 fixes 9 bugs.

22 Jul 2025
Biztonsági szemle
ISC Stormcast For Tuesday, July 22nd, 2025 https://isc.sans.edu/podcastdetail/9536, (Tue, Jul 22nd)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.

22 Jul 2025
Biztonsági szemle
Country Digital Acceleration: Shaping Spain’s digital future
Country Digital Acceleration is powering Spain’s digital future—building skills, innovation, and secure infrastructure for a more connected nation.

21 Jul 2025
Biztonsági szemle
Human Digital Twins Could Give Attackers a Dangerous Advantage
While this emerging technology offers many benefits, digital twins also have several drawbacks, as these convincing impersonations can be used in social engineering attacks.

21 Jul 2025
Biztonsági szemle
Malicious Implants Are Coming to AI Components, Applications
A red teamer is publishing research next month about how weaknesses in modern security products lay the groundwork for stealthy implants in AI-powered applications.

21 Jul 2025
Biztonsági szemle
Europol Sting Leaves Russian Cybercrime's 'NoName057(16)' Group Fractured
National authorities have issued seven arrest warrants in total relating to the cybercrime collective known as NoName057(16), which recruits followers to carry out DDoS attacks on perceived enemies of Russia.
21 Jul 2025
Biztonsági szemle
TAG Bulletin: Q2 2025
Our bulletin covering coordinated influence operation campaigns terminated on our platforms in Q2 2025.

21 Jul 2025
Biztonsági szemle
Microsoft Rushes Emergency Patch for Actively Exploited SharePoint 'ToolShell' Bug
Malicious actors already have already pounced on the zero-day vulnerability, tracked as CVE-2025-53770, to compromise US government agencies and other businesses in ongoing and widespread attacks.

21 Jul 2025
Biztonsági szemle
Containment as a Core Security Strategy
We cannot keep reacting to vulnerabilities as they emerge. We must assume the presence of unknown threats and reduce the blast radius that they can affect.
Pagination
- Previous page ‹‹
- Page 185
- Next page ››