Security Bulletin

15 Jul 2025
Biztonsági szemle
Keylogger Data Stored in an ADS, (Tue, Jul 15th)
If many malware samples try to be "filess" (read: they try to reduce their filesystem footprint to the bare minimum), another technique remains interesting: Alternate Data Streams or "ADS"[ 1]. This NTFS feature allows files to contain multiple data...

15 Jul 2025
Biztonsági szemle
ISC Stormcast For Tuesday, July 15th, 2025 https://isc.sans.edu/podcastdetail/9526, (Tue, Jul 15th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.

14 Jul 2025
Biztonsági szemle
Web-Inject Campaign Debuts Fresh Interlock RAT Variant
A cyber-threat campaign is using legitimate websites to inject victims with remote access Trojans belonging to the Interlock ransomware group, in order to gain control of devices.

14 Jul 2025
Biztonsági szemle
Military Veterans May Be What Cybersecurity Is Looking For
As the field struggles with a shortage, programs that aim to provide veterans with the technical skills needed to succeed in cybersecurity may be the solution for everyone.

14 Jul 2025
Biztonsági szemle
Google Gemini AI Bug Allows Invisible, Malicious Prompts
A prompt-injection vulnerability in the AI assistant allows attackers to create messages that appear to be legitimate Google Security alerts but instead can be used to target users across various Google products with vishing and phishing.
14 Jul 2025
Biztonsági szemle
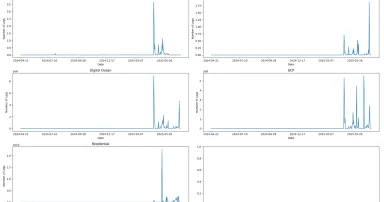
DShield Honeypot Log Volume Increase, (Mon, Jul 14th)
The volume of honeypot logs changes over time. Very rarely are honeypot logs quiet, meaning that there are no internet scans or malicious activity generating logs. Honeypots can see large increases in activity [1], but this has tended to be the...

14 Jul 2025
Biztonsági szemle
The Dark Side of Global Power Shifts & Demographic Decline
As global power realigns and economies falter, the rise in cybercrime is no longer hypothetical — it's inevitable.

14 Jul 2025
Biztonsági szemle
From classroom to career: Ghana’s new gateway to tech success
Cisco's collaboration with BASICS International launched the Chorkor Digital Lab in Ghana, empowering students with tech skills for careers in cybersecurity and networking, with support from Cisco Networking Academy and the Technology Grant Program.

14 Jul 2025
Biztonsági szemle
ISC Stormcast For Monday, July 14th, 2025 https://isc.sans.edu/podcastdetail/9524, (Mon, Jul 14th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.

14 Jul 2025
Biztonsági szemle
Experimental Suspicious Domain Feed, (Sun, Jul 13th)
We have had a "newly registered domain" feed for a few years. This feed pulls data from ICANN's centralized zone data service ( https://czds.icann.org) and TLS certificate transparency logs.

11 Jul 2025
Biztonsági szemle
Pay2Key Ransomware Gang Resurfaces With Incentives to Attack US, Israel
The ransomware-as-a-service (RaaS) operation, which has been tied to an Iranian advanced persistent threat (APT) group, recently boosted its affiliate profit share to 80% for attacks on Western targets.

11 Jul 2025
Biztonsági szemle
350M Cars, 1B Devices Exposed to 1-Click Bluetooth RCE
Mercedes, Skoda, and Volkswagen vehicles, as well as untold industrial, medical, mobile, and consumer devices, may be exposed to a vulnerable Bluetooth implementation called "PerfektBlue."
Pagination
- Previous page ‹‹
- Page 190
- Next page ››