Security Bulletin

16 Apr 2026
Biztonsági szemle
From Connectivity to Security: How E80 Future-proofed its AGV Operations with Cisco
Autonomous vehicles. Complex factories. Rising cyber threats. Discover how E80 tackled all three with Cisco industrial networking.

16 Apr 2026
Biztonsági szemle
The Infrastructure of a Floating City: AIDA Cruises’ CX-Led Digital Transformation
Discover how Cisco CX transformed AIDA Cruises’ digital infrastructure, delivering secure, scalable connectivity and AIOps for an unparalleled guest experience.

16 Apr 2026
Biztonsági szemle
Two-Factor Authentication Breaks Free from the Desktop
Threat actors know how to bypass security systems outside of traditional IT environments. Implementing 2FA could provide a needed extra security barrier in the physical world.

16 Apr 2026
Biztonsági szemle
Microsoft's Original Windows Secure Boot Certificate Is Expiring
The Secure Boot refresh is one of the largest coordinated security maintenance efforts across the Windows ecosystem, Microsoft said. Update those PCs soon.

16 Apr 2026
Biztonsági szemle
Scaling your network for AI without a forklift upgrade
Scale infrastructure without costly upgrades using an autonomous, software-defined network model that protects existing investments.

16 Apr 2026
Biztonsági szemle
Why modern networks are moving DDoS defense to the edge
Fortify your network edge against evolving DDoS threats. Discover how Cisco Secure DDoS Edge Protection transforms network security by moving mitigation directly to the edge—and how it can help you slash TCO by 60%.

16 Apr 2026
Biztonsági szemle
Evolve IP Media to AI-Driven Media Fabrics: Future-Proof Broadcast with Cisco and NVIDIA
AI is revolutionizing live broadcast, but it demands a network built for heavy lifting. Read how Cisco and NVIDIA are teaming up to power scalable, high-performance media production.

16 Apr 2026
Biztonsági szemle
Cisco and Generation are scaling AI-powered pathways to employment
Learn how Cisco and Generation partner to build digital pathways to employment, using AI to connect job seekers with relevant careers and industry-recognized credentials.

16 Apr 2026
Biztonsági szemle
6-Year Ransomware Campaign Targets Turkish Homes & SMBs
While enterprises breaches make more headlines, smaller incidents tend to be under-reported, if at all, allowing campaigns to last longer with less disruption.

16 Apr 2026
Biztonsági szemle
ISC Stormcast For Thursday, April 16th, 2026 https://isc.sans.edu/podcastdetail/9894, (Thu, Apr 16th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
16 Apr 2026
Biztonsági szemle
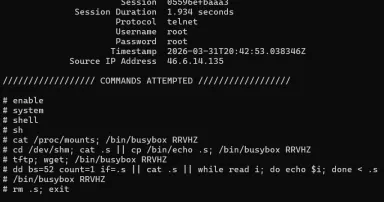
[Guest Diary] Compromised DVRs and Finding Them in the Wild, (Thu, Apr 16th)
[This is a Guest Diary by Alec Jaffe, an ISC intern as part of the SANS.edu Bachelor's Degree in Applied Cybersecurity (BACS) program [1].

15 Apr 2026
Biztonsági szemle
Critical MCP Integration Flaw Puts NGINX at Risk
Attackers can abuse the near-maximum severity flaw in nginx-ui to restart, create, modify, and delete NGINX configuration files.
Pagination
- Previous page ‹‹
- Page 20
- Next page ››