Security Bulletin

21 May 2025
Biztonsági szemle
Unimicron, Presto Attacks Mark Industrial Ransomware Surge
A number of major industrial organizations suffered ransomware attacks last quarter, such as PCB manufacturer Unimicron, appliance maker Presto, and more — a harbinger of a rapidly developing and diversifying threat landscape.

21 May 2025
Biztonsági szemle
Apparent ransomware attack leads to systemwide outage for Kettering Health
Kettering operates 14 medical centers and more than 120 outpatient locations in western Ohio.

21 May 2025
Biztonsági szemle
Coinbase Breach Compromises Nearly 70K Customers' Information
Coinbase asserts that this number is only a small fraction of the number of its verified users, though it's still offering a $20 million reward to catch the criminals.

21 May 2025
Biztonsági szemle
Unpatched Windows Server Flaw Threatens Active Directory Users
Attackers can exploit a vulnerability present in the delegated Managed Service Account (dMSA) feature that fumbles permission handling and is present by default.

21 May 2025
Biztonsági szemle
NIST's 'LEV' Equation to Determine Likelihood a Bug Was Exploited
The new equation, introduced by the National Institute of Standards and Technology (NIST), aims to offer a mathematical likelihood index that could be a game-changer for SecOps teams and vulnerability patch prioritization.
21 May 2025
Biztonsági szemle
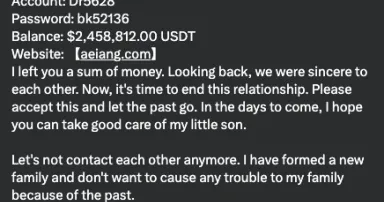
New Variant of Crypto Confidence Scam, (Wed, May 21st)
In February, we had a few diaries about crypto wallet scams. We saw these scams use YouTube comments, but they happened via other platforms and messaging systems, not just YouTube [1]. The scam was a bit convoluted: The scammer posted the secret key...

21 May 2025
Biztonsági szemle
The Hidden Cybersecurity Risks of M&A
Merger and acquisition due diligence typically focuses on financials, legal risks, and operational efficiencies. Cybersecurity is often an afterthought — and that's a problem.

21 May 2025
Biztonsági szemle
Dark Reading Confidential: The Day I Found an APT Group in the Most Unlikely Place
Dark Reading Confidential Episode 6: Threat hunters Ismael Valenzuela and Vitor Ventura share stories about the tricks they used to track down advanced persistent threat groups, and the surprises they discovered along the way.

21 May 2025
Biztonsági szemle
Connecting a New Generation of Moving Assets with Cisco Ultra-Reliable Wireless Backhaul
Aterpa leverages Ultra-Reliable Wireless Backhaul (URWB) for teleremote operations, ensuring the safe decommissioning of dams.

21 May 2025
Biztonsági szemle
Strider launches real-time threat detection upgrades
SiliconANGLE reports that Strider Technologies has rolled out major enhancements to its AI-powered threat intelligence engine, Spark, aiming to help organizations counter threats from state-sponsored actors with greater speed and accuracy.

21 May 2025
Biztonsági szemle
China-linked operative exposed at U.S. university
An investigation has revealed that a Chinese intelligence agent posing as a Stanford University student attempted to infiltrate academic circles researching China-related issues and advanced technologies, including artificial intelligence, reports...

21 May 2025
Biztonsági szemle
Survey finds gaps in cyber threat intel sharing
A new survey conducted by Cyware at the RSA Conference 2025 highlights a significant disconnect between cybersecurity professionals belief in collaboration and the operational reality of threat intelligence sharing, according to BetaNews.
Pagination
- Previous page ‹‹
- Page 268
- Next page ››