Security Bulletin

15 Jan 2026
Biztonsági szemle
Winter Olympics Could Share Podium With Cyberattackers
The upcoming Winter Games in the Italian Alps are attracting both hacktivists looking to reach billions of people and state-sponsored cyber-spies targeting the attending glitterati.
15 Jan 2026
Biztonsági szemle
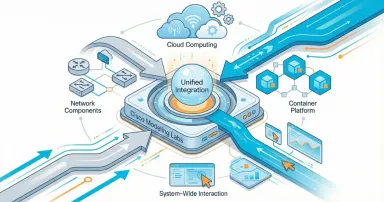
Building Custom Containers for Cisco Modeling Labs (CML): A Practical Guide
Learn how to build custom containers for Cisco Modeling Labs to unlock advanced testing, automation, and distributed system modeling.

15 Jan 2026
Biztonsági szemle
Navigating Firewall Migrations: Best Practices and Palo Alto to Cisco Next-Gen Firewall Specifics
Walk through the complex undertaking of migrating firewalls from Palo Alto Networks to Cisco Next-Generation Firewalls.

15 Jan 2026
Biztonsági szemle
Parking Pains? Not Anymore! See how HL Robotics and Cisco can help
HL Robotics’ Parkie and Cisco URWB tech deliver seamless, automated parking—maximizing convenience, reliability, and efficiency for all.

15 Jan 2026
Biztonsági szemle
Vulnerabilities Surge, But Messy Reporting Blurs Picture
MITRE loses its lead as the top reporter of vulnerabilities, while new organizations pump out CVEs and reported bugs in WordPress plug-ins surge.

15 Jan 2026
Biztonsági szemle
BIND statement forwarders
Name forwarders Syntax forwarders { ; [ ;...] }; Blocks options Default value(s) There are no default acls defined Introduced Date: 1997-05-06 BIND version: 8.1.1 Deprecated Still current as of 2025-11-24 Description The forwarders statement allows...
15 Jan 2026
Biztonsági szemle
Cisco’s Journey in AI Workforce Transformation
Cisco’s latest AI research reveals how AI is reshaping the way Cisco employees work—and what that means for individual and team engagement, performance, career growth, and leadership.

15 Jan 2026
Biztonsági szemle
Trio of Critical Bugs Spotted in Delta Industrial PLCs
Experts disagree on whether the vulnerabilities in a programmable logic controller from Delta are a five-alarm fire or not much to worry over.

14 Jan 2026
Biztonsági szemle
Retail, Services Industries Under Fire in Oceania
Last year in Australia, New Zealand, and the South Pacific, Main Street businesses like retail and construction suffered more cyberattacks than their critical sector counterparts.

14 Jan 2026
Biztonsági szemle
Microsoft Disrupts Cybercrime Service RedVDS
RedVDS, a cybercrime-as-a-service operation that has stolen millions from victims, lost two domains to a law enforcement operation supported by Microsoft.

14 Jan 2026
Biztonsági szemle
Cisco Launches Global Threat Modeling Security Assessment Service for Threat-Informed Defense
In today’s threat landscape, resilience depends on understanding how your adversaries operate as well as understanding your own environment. Learn about Cisco Threat Modeling today.

14 Jan 2026
Biztonsági szemle
Cisco AI Summit will define what comes next
Cisco AI Summit brings together Jensen Huang, Sam Altman, Matt Garman, Marc Andreessen, Dr. Fei-Fei Li, and more to define how artificial intelligence will reshape business and society.
Pagination
- Previous page ‹‹
- Page 73
- Next page ››