Security Bulletin

5 Aug 2024
Biztonsági szemle
Malware distributed through ISP compromise
After conducting a DNS poisoning attack against the ISP, StormBamboo leveraged vulnerable HTTP software update mechanisms without digital signature validation to facilitate the installation of MACMA and MgBot malware to Windows and macOS systems.
5 Aug 2024
Biztonsági szemle
Navigating the GRC landscape: Insights from Mark Weatherford, former deputy under secretary for cybersecurity
Mark Weatherford, a seasoned cybersecurity professional with a distinguished career in both the public and private sectors, shares his perspectives on the evolving landscape of governance, risk management, and compliance (GRC).

5 Aug 2024
Biztonsági szemle
How Regional Regulations Shape Global Cybersecurity Culture
Ultimately, a more cyber-secure world requires a global governing body to regulate and campaign for cybersecurity, with consistent regulatory requirements in the various regions around the world.
5 Aug 2024
Biztonsági szemle
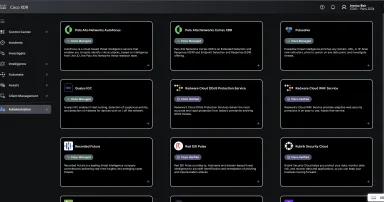
Cisco XDR: Open Ecosystem Accelerated at Black Hat Events
Cisco XDR turns one year old. Here is the backstory of how we developed relationships and alliances with “competitors” to have the open ecosystem of today.
5 Aug 2024
Biztonsági szemle
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. CVE-2018-0824 Microsoft COM for Windows Deserialization of Untrusted Data Vulnerability These types of vulnerabilities are...

5 Aug 2024
Biztonsági szemle
Russia's 'Fighting Ursa' APT Uses Car Ads to Install HeadLace Malware
The scheme, from the group also known as APT28, involves targeting Eastern European diplomats in need of personal transportation and tempting them with a purported good deal on a Audi Q7 Quattro SUV.

5 Aug 2024
Biztonsági szemle
How early adopters drive security innovation
While bringing on an early-adopter security tool presents some risk for a CISO, it’s often a good choice for the right organization.

5 Aug 2024
Biztonsági szemle
Microsoft Bounty Program Year in Review: $16.6M in Rewards
We are excited to announce that this year the Microsoft Bounty Program has awarded $16.6M in bounty awards to 343 security researchers from 55 countries, securing Microsoft customers in partnership with the Microsoft Security Response Center (MSRC)...
5 Aug 2024
Biztonsági szemle
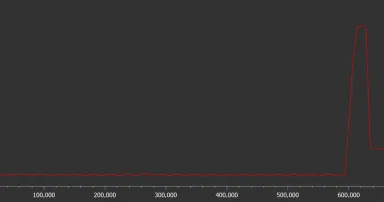
Script obfuscation using multiple instances of the same function, (Mon, Aug 5th)
Threat actors like to make detection and analysis of any malicious code they create as difficult as possible â for obvious reasons. There are any number of techniques which they may employ in this area, nevertheless, the one approach, that is...

5 Aug 2024
Biztonsági szemle
ISC Stormcast For Monday, August 5th, 2024 https://isc.sans.edu/podcastdetail/9082, (Mon, Aug 5th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
4 Aug 2024
Biztonsági szemle
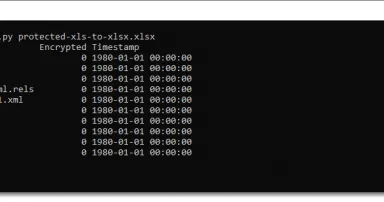
OOXML Spreadsheets Protected By Verifier Hashes, (Sat, Aug 3rd)
When I wrote about the internal file format of protected spreadsheets, I mentioned a simple 16-bit hash for .xls files in diary entry " 16-bit Hash Collisions in .xls Spreadsheets" and a complex hash based on SHA256 for .xlsx files in diary entry "...

3 Aug 2024
Biztonsági szemle
Planning for Cisco Certification Exam Success
Plan your route to Cisco certification success with insights, tips, and advice from our experts.
Pagination
- Previous page ‹‹
- Page 729
- Next page ››