Security Bulletin

4 May 2026
Biztonsági szemle
Galaxy Mode is live: A limited-time look at what your Cisco AI Assistant and AgenticOps can already do
This May the 4th, we’re bringing Galaxy Mode to the Cisco AI Assistant. Troubleshoot network issues, create workflows, and more with an engaging, limited-time experience.

4 May 2026
Biztonsági szemle
Securing the Agentic Workforce: Cisco Announces Intent to Acquire Astrix Security
Cisco announces its intent to acquire Astrix Security, extending Zero Trust to the agentic workforce to secure non-human identities and AI agents in the modern enterprise.

4 May 2026
Biztonsági szemle
Understanding CISA BOD 26-02: Mitigating Risk from End-of-Support Edge Devices
Learn how Cisco’s FedRAMP-authorized solutions help federal agencies meet the new CISA BOD 26-02 requirements by effectively mitigating the security risks associated with End-of-Support edge devices.

4 May 2026
Biztonsági szemle
How Dark Reading Lifted Off the Launchpad in 2006
Twenty years ago, this media brand didn't have a print edition to attract eyeballs and sponsors. Top-notch content and editorial talent did the heavy lifting.

4 May 2026
Biztonsági szemle
ISC Stormcast For Monday, May 4th, 2026 https://isc.sans.edu/podcastdetail/9916, (Mon, May 4th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.

3 May 2026
Biztonsági szemle
Wireshark 4.6.5 Released, (Sun, May 3rd)
Wireshark release 4.6.5 fixes 43 vulnerabilities (38 CVEs) and 35 bugs.

1 May 2026
Biztonsági szemle
76% of All Crypto Stolen in 2026 Is Now in North Korea
North Korean threat actors are pulling off historic cryptocurrency heists on a yearly, sometimes weekly basis now. AI might be helping them.
1 May 2026
Biztonsági szemle
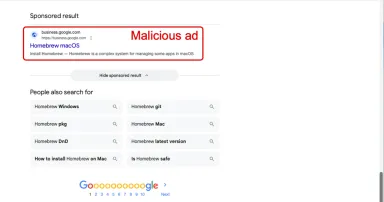
Malicious Ad for Homebrew Leads to MacSync Stealer, (Fri, May 1st)
Introduction

1 May 2026
Biztonsági szemle
If AI's So Smart, Why Does It Keep Deleting Production Databases?
The issue isn't artificial intelligence, but rather an industry adding AI agent integrations into production environments before proper security testing.

1 May 2026
Biztonsági szemle
Digging Deeper: The Future of Mining with Automation and Ultra-Reliable Wireless
Explore the future of mining with automation. Learn how Cisco’s ultra-reliable wireless technology provides the connectivity needed for safe, 24/7 autonomous operations.

1 May 2026
Biztonsági szemle
Name That Toon: Mark of (Security) Progress
Feeling creative? Have something to say about the last 20 years of cybersecurity? Our editors will award the best cybersecurity-related caption with a $20 gift card.

1 May 2026
Biztonsági szemle
20 Years in Cyber: Dark Reading Marks Milestone With Month of Special Coverage
On this day in 2006, Dark Reading went live. We have a celebration planned that spans our two decades of covering the industry, and you, dear readers, are invited.
Pagination
- Previous page ‹‹
- Page 10
- Next page ››