Security Bulletin

9 Jan 2024
Biztonsági szemle
Hacked YouTube channels leveraged for Lumma Stealer distribution
Hacked YouTube channels leveraged for Lumma Stealer distribution Several YouTube channels have been compromised to enable the distribution of the Lumma Stealer information-stealing malware via videos purporting to share cracked versions of legitimate...

9 Jan 2024
Biztonsági szemle
Crypto drainers spread via hijacked Netgear, Hyundai X accounts
BleepingComputer reports that Netgear and Hyundai Middle East & Africa had their official accounts on X, formerly Twitter, compromised to facilitate the distribution of cryptocurrency wallet drainer malware.

9 Jan 2024
Biztonsági szemle
New Silver RAT malware actively peddled to cybercriminals
Newly emergent stealthy remote access trojan Silver RAT has been aggressively marketed by suspected Syrian threat operation Anonymous Arabic across various social media and hacking sites, reports The Hacker News.

9 Jan 2024
Biztonsági szemle
Novel CI/CD attack could prompt widespread supply chain compromise
Significant supply chain compromise could be conducted against major IT and cryptocurrency organizations through a novel continuous integration/continuous delivery attack technique exploiting thousands of public GitHub repositories with malicious...

9 Jan 2024
Biztonsági szemle
Ransomware Gang Gives Toronto Zoo the Monkey Business
As the investigation continues, the zoo reports that it does not store the credit card information of its guests.

9 Jan 2024
Biztonsági szemle
Turkish Cyber Threat Targets MSSQL Servers With Mimic Ransomware
Microsoft's database continues to attract cybercriminal attention; the nature of this wave's threat group is unknown, with the attacks having been exposed only after a happenstance OpSec lag.
9 Jan 2024
Biztonsági szemle
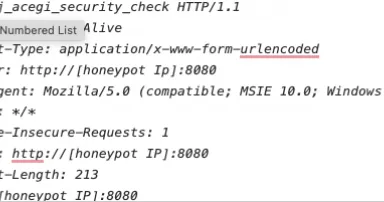
Jenkins Brute Force Scans, (Tue, Jan 9th)
Our honeypots saw a number of scans for "/j_acegi_security_check" the last two days. This URL has not been hit much lately, but was hit pretty hard last March. The URL is associated with Jenkins, and can be used to brute force passwords.

9 Jan 2024
Biztonsági szemle
Leveraging a digital twin with machine learning to revitalize bridges
Learn how the University of the Bundeswehr Munich used Cisco technology to develop a digital twin model for bridges that predicts maintenance windows based on telemetry, reducing costs and optimizing the design of new bridges with real data rather...

9 Jan 2024
Biztonsági szemle
High-severity RCE among 6 bugs added to CISA's exploited vulnerability catalog
Some of the most dangerous vulnerabilities of 2023 make it to CISA's KEV list, including bugs in Apple and Apache products.

9 Jan 2024
Biztonsági szemle
Bangladesh Election App Crashes Amid Suspected Cyberattack
The country's election commission pointed the blame at traffic coming from Ukraine and Germany.
9 Jan 2024
Biztonsági szemle
Beware Weaponized YouTube Channels Spreading Lumma Stealer
Videos promoting how to crack popular software circumvent Web filters by using GitHub and MediaFire to propagate the malware.
Pagination
- Previous page ‹‹
- Page 1137
- Next page ››
