Security Bulletin
26 Apr 2025
Biztonsági szemle
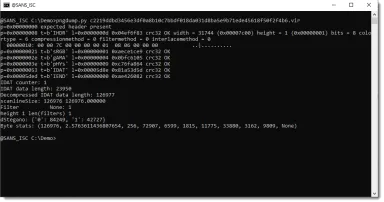
Steganography Analysis With pngdump.py, (Sat, Apr 26th)
I like it when a diary entry like " Example of a Payload Delivered Through Steganography" is published: it gives me an opportunity to test my tools, in particular pngdump.py, a tool to analyze PNG files.

25 Apr 2025
Biztonsági szemle
Microsoft Office 365 MFA targeted by ‘SessionShark’ phishing kit
The malicious service is advertised to evade detection and closely mimic a real login page.
25 Apr 2025
Biztonsági szemle
Beating the AI Game, Ripple, Numerology, Darcula, Special Guests from Hidden Layer... - Malcolm Harkins, Kasimir Schulz - SWN #471

25 Apr 2025
Biztonsági szemle
Girls Power Tech Inspires the Next Generation of Tech Leaders
Cisco Networking Academies across North Texas gathered for this year's Girls Power Tech event, held at the Cisco Richardson campus on April 17, 2025.

25 Apr 2025
Biztonsági szemle
SAP patches zero day rated 10.0 in NetWeaver
Attackers observed exploiting vulnerability in SAP's NetWeaver Visual Composer product.

25 Apr 2025
Biztonsági szemle
Identity and Access Management to steal the spotlight at RSAC 2025
Emerging identity and access management tools and approaches will be a hot topic this year.

25 Apr 2025
Biztonsági szemle
Mobile Applications: A Cesspool of Security Issues
An analysis of more than a half-million mobile apps find encryption problems, privacy issues, and known vulnerabilities in third-party code. What can users and developers do?

25 Apr 2025
Biztonsági szemle
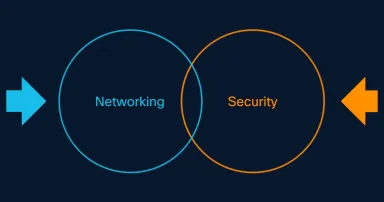
Navigating the 8D city: Why multi-dimensional network security is no longer optional
The future of network security lies in a combination of cornerstone capabilities that combine to provide multi-dimensional, holistic protection.
25 Apr 2025
Biztonsági szemle
Why a Distributed Workforce Needs Distributed Security
Learn how to overcome external network dependencies and build digital resilience with Cisco secure access service edge (SASE).

25 Apr 2025
Biztonsági szemle
How Organizations Can Leverage Cyber Insurance Effectively
By focusing on prevention, education, and risk transfer through insurance, organizations — especially SMEs — can protect themselves from the rapidly escalating threats of cyberattacks.

25 Apr 2025
Biztonsági szemle
Consolidated global cyber regulations sought by CISO coalition
Members of the Group of Seven nations and the Organization for Economic Cooperation and Development have been urged by a coalition of chief information security officers from 45 major firms, including Amazon Web Services, Mastercard, and Honeywell...
25 Apr 2025
Biztonsági szemle
South Korea: Unauthorized user data transfer conducted by DeepSeek
CNBC reports that Chinese artificial intelligence startup DeepSeek was found by South Korea's Personal Information Protection Commission to have moved user data to multiple China- and U.S.-based firms without necessary consent and disclosures as part...
Pagination
- Previous page ‹‹
- Page 308
- Next page ››