Security Bulletin

19 Jan 2025
Biztonsági szemle
Zero Trust and Entra ID Conditional Access, (Sun, Jan 19th)
Microsoft Entra ID (Formerly Azure AD) Conditional Access (CA) policies are the key components to a Zero Trust strategy, as it provides the ability to function as the front door for users and devices. CA policies use attributes, or signals, of...
18 Jan 2025
Biztonsági szemle
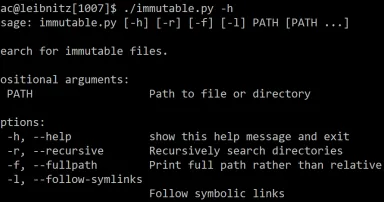
New tool: immutable.py, (Sat, Jan 18th)
When performing triage on a Linux system you suspect might be compromised, there are many aspects of the system that you may want to look at. In SANS FOR577, we talk about some existing tools and even writing your own bash script to collect triage...

18 Jan 2025
Biztonsági szemle
‘Sneaky Log’ phishing kits slip by Microsoft 365 accounts
Phishing-as-a-Service kits intercept user credentials and 2FA, bypassing many email and secure web gateways.

17 Jan 2025
Biztonsági szemle
Feds worry AT&T breach could out informants
The FBI is reportedly in a panic over a possible leak of informant data thanks to an AT&T data breach
17 Jan 2025
Biztonsági szemle
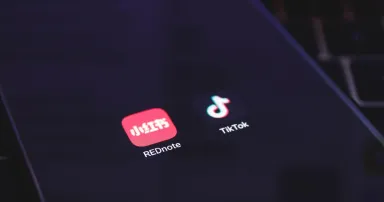
Has the TikTok Ban Already Backfired on US Cybersecurity?
The Supreme Court has affirmed TikTok's ban in the US, which has its users in revolt and is creating a whole new set of national cybersecurity concerns.
17 Jan 2025
Biztonsági szemle
AIs in Love, UEFI, Fortinet, Godaddy, Juggalos, Aaran Leyland, and More. - SWN #443

17 Jan 2025
Biztonsági szemle
TikTok’s national security risk warrants ban, Supreme Court rules
The ruling could have implications for other foreign-owned applications.

17 Jan 2025
Biztonsági szemle
Employees Enter Sensitive Data Into GenAI Prompts Far Too Often
The propensity for users to enter customer data, source code, employee benefits information, financial data, and more into ChatGPT, Copilot, and others is racking up real risk for enterprises.

17 Jan 2025
Biztonsági szemle
15K Fortinet Device Configs Leaked to the Dark Web
The stolen firewall data is thorough but more than 2 years old now, meaning that most organizations following even basic security practices face minimal risk, hopefully.
17 Jan 2025
Biztonsági szemle
US Sanctions Chinese Hacker & Firm for Treasury, Critical Infrastructure Breaches
The cyber actor played a role in the Treasury breach as well as attacks on critical infrastructure, linked to China-backed advanced persistent threat (APT) group Salt Typhoon.

17 Jan 2025
Biztonsági szemle
Leveraging Behavioral Insights to Counter LLM-Enabled Hacking
As LLMs broaden access to hacking and diversify attack strategies, understanding the thought processes behind these innovations will be vital for bolstering IT defenses.

17 Jan 2025
Biztonsági szemle
Additional US sanctions issued to clampdown North Korean IT worker scam
The U.S. has continued its crackdown against North Korean IT worker scams with sanctions against the country's government weapons trading office Department 53 and its Laos-based front companies Korea Osong Shipping and Chonsurim Trading Corporation...
Pagination
- Previous page ‹‹
- Page 470
- Next page ››