Biztonsági szemle

2026. május 15.
Biztonsági szemle
Taiwan Incident Highlights Cybersecurity Gaps in Rail Systems
A Taiwanese student experimenting with software-defined radio technology shut down three bullet trains for nearly an hour, leading to an anti-terrorism response.

2026. május 15.
Biztonsági szemle
Accelerate Your Career and Impact with CCNA Certifications
Align your professional growth with your personal values. Choose the CCNA certification that not only sustains your future—but powers the world.
2026. május 14.
Biztonsági szemle
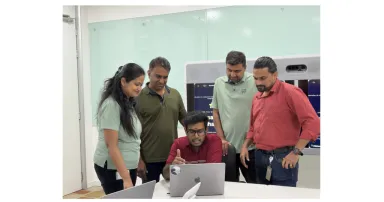
Skills-based volunteering for the AI era: Inside Cisco’s first Tech for Social Good Hackathon
During our first Tech for Social Good Hackathon, Cisco experts developed AI solutions to real problems facing our nonprofit partners. Learn what happened inside the build — and why skills-based volunteering is a model worth scaling.

2026. május 14.
Biztonsági szemle
SecurityScorecard Snags Driftnet to Level Up Threat Intelligence
The acquisition looks to boost visibility into third-party ecosystems, which are becoming a bigger concern as vectors for supply chain attacks.

2026. május 14.
Biztonsági szemle
Maximum Severity Cisco SD-WAN Bug Exploited in the Wild
This is the second time this year a threat actor has leveraged a CVSS 10.0 vulnerability in Cisco's network control system.

2026. május 14.
Biztonsági szemle
Congress Puts Heat on Instructure After Canvas Outage
The House Committee on Homeland Security sent a letter about the Canvas cyberattack, the same day that the edtech company said it reached an "agreement" with the ShinyHunters cybercriminals.

2026. május 14.
Biztonsági szemle
Cisco Live 2026: Bringing the Future of Customer Experience to Las Vegas
Check out a preview of CX at Cisco Live 2026!

2026. május 14.
Biztonsági szemle
'FrostyNeighbor' APT Carefully Targets Govt Orgs in Poland, Ukraine
Attackers uniquely fingerprint victims before delivering spear-phishing payloads aimed at espionage, in the latest campaign from the Belarussian nation-state threat group.

2026. május 14.
Biztonsági szemle
Mission-First: Equipping the Digital Warfighter at AFCEA TechNet Cyber 2026
Discover how we are fortifying the digital battleground with secure AI and quantum-resilient networks, and get the full details on our upcoming demonstrations at TechNet Cyber in Baltimore this June.

2026. május 14.
Biztonsági szemle
Edge opportunity for service providers: Turn infrastructure into new services
The edge is becoming a platform for distributed applications and enterprise services. That shift is opening a new opportunity for service providers: delivering compute and intelligence alongside their connectivity offerings.

2026. május 14.
Biztonsági szemle
MRC and SRv6: How Foundational Networking Innovations Are Enabling the Next Generation of AI Supercomputers
The Multipath Reliable Connection (MRC) protocol marks a leap in AI infrastructure. By leveraging Cisco-pioneered SRv6, MRC enables near-perfect uptime and full bisection bandwidth at the scale of 100,000+ GPUs, powering the next generation of AI.

2026. május 14.
Biztonsági szemle
The SMB Marketing Reset: Winning Customer Trust in a Digital-First Economy
In a changing digital landscape, discover how small and medium-sized businesses, both B2B and B2C, are building trust with customers through personalized and creative marketing strategies.
Oldalszámozás
- Előző oldal ‹‹
- 2. oldal
- Következő oldal ››