Biztonsági szemle
2026. április 17.
Biztonsági szemle
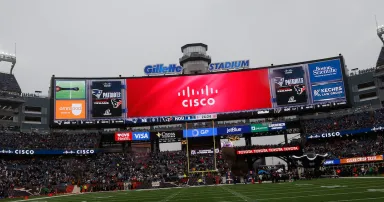
Unlocking the Future of Fan Engagement: The Power of VisionEDGE
VisionEDGE, a Cisco and Wipro collaboration, powers next-gen venues with intelligent digital signage and IPTV. It integrates with Cisco’s network to deliver personalized fan experiences, 4K streaming, and AI-driven content for global venues.
2026. április 17.
Biztonsági szemle
Find Yourself in the Future: AI Is the New Baseline—Here’s How to Build Your Skills
AI literacy is your career edge. Get key takeaways from Cisco NetAcad's latest Find Yourself in the Future session—plus free courses to build your AI skills today.

2026. április 17.
Biztonsági szemle
Every Old Vulnerability Is Now an AI Vulnerability
AI's danger isn't that it's creating new bugs, it's that it's amplifying old ones.

2026. április 17.
Biztonsági szemle
One Day with Our Customers: Driving better outcomes through customer centricity
Cisco employees across every function spent time onsite learning how customers’ businesses actually run.

2026. április 17.
Biztonsági szemle
What It Really Takes to Build an AI-First Workforce
Adele Trombetta led her team through a major AI transformation. Read her advice on building an AI-ready culture, driving innovation, and empowering your people.

2026. április 17.
Biztonsági szemle
Coast Guard's New Cybersecurity Rules Offers Lessons for CISOs
The Maritime Transportation Security Act (MTSA) requires plans to protect OT systems, audits by independent third parties, and a hybrid OT-security role.

2026. április 17.
Biztonsági szemle
Sajtószemle – 2026. 16. hét
Megjelent a 2026. 16. hetére vonatkozó hírválogatás, amely az NBSZ NKI által 2026.04.10. és 2026.04.16. között kezelt incidensek, valamint az elosztott kormányzati IT biztonsági csapdarendszerből (GovProbe1) származó adatok statisztikai eloszlását is...

2026. április 17.
Biztonsági szemle
ISC Stormcast For Friday, April 17th, 2026 https://isc.sans.edu/podcastdetail/9896, (Fri, Apr 17th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
2026. április 17.
Biztonsági szemle
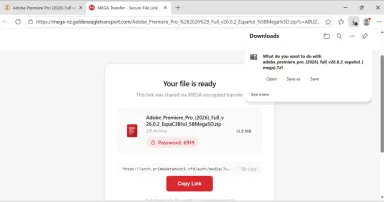
Lumma Stealer infection with Sectop RAT (ArechClient2), (Fri, Apr 17th)
Introduction

2026. április 16.
Biztonsági szemle
NIST Revamps CVE Framework to Focus on High-Impact Vulnerabilities
The National Institute of Standards and Technology carved a new path for vulnerability remediation by changing the way it prioritizes software flaws.

2026. április 16.
Biztonsági szemle
North Korea Uses ClickFix to Target macOS Users' Data
Sapphire Sleet uses fake job offers and phony Zoom updates to deliver ClickFix attacks that steal credentials and sensitive data from Macs.

2026. április 16.
Biztonsági szemle
'Harmless' Global Adware Transforms Into an AV Killer
A benign looking update Dragon Boss pushed out in March 2025 established persistence via scheduled tasks and arranged for future payloads to be excluded from Windows Defender.
Oldalszámozás
- Előző oldal ‹‹
- 19. oldal
- Következő oldal ››