Biztonsági szemle

2025. július 24.
Biztonsági szemle
Law Enforcement Cracks Down on XSS — but Will It Last?
The arrest of a suspected administrator for the popular cybercrime forum was one of several enforcement actions in the past week targeting malicious activity.

2025. július 24.
Biztonsági szemle
Ransomware Actors Pile on 'ToolShell' SharePoint Bugs
Storm-2603, a China-based threat actor, is targeting SharePoint customers in an ongoing ransomware campaign.

2025. július 24.
Biztonsági szemle
Splunk and Fast Forward partner to empower AI-driven nonprofits
Splunk has teamed up with Fast Forward to empower a new generation of AI-driven nonprofits tackling critical global issues in health, climate, and education. This partnership highlights how ethical, collaborative, and inclusive AI innovation can...

2025. július 24.
Biztonsági szemle
Host reservations deleted when editing shared networks with Stork
One of Stork's features is the ability to edit shared networks in Kea DHCP, and shared networks that contain subnets can support host reservations. However, due to a bug in Stork, if you edit a shared network in Stork that contains a subnet, any host...

2025. július 24.
Biztonsági szemle
CVE-2025-40777: A possible assertion failure when using the 'stale-answer-client-timeout 0' option
CVE: CVE-2025-40777 Document version: 2.0 Posting date: 16 July 2025 Program impacted: BIND Versions affected: BIND 9.20.0 -> 9.20.10 9.21.0 -> 9.21.9 (Versions prior to 9.18.0 were not assessed.) BIND Supported Preview Edition 9.20.9-S1 -> 9.20.10...

2025. július 24.
Biztonsági szemle
Translating Cyber-Risk for the Boardroom
When security leaders embrace this truth and learn to speak in the language of leadership, they don't just protect the enterprise, they help lead it forward.

2025. július 24.
Biztonsági szemle
Empowering Higher Education: Cisco’s Perspective on the CAUDIT Top Ten 2025 Technology Priorities
At Cisco, we believe that technology is the foundation of innovation, collaboration, and success in higher education and research. The release of the CAUDIT Top Ten 2025 report is a pivotal moment for institutions across Australasia and the South...
2025. július 24.
Biztonsági szemle
Cisco Secure Firewall: First to earn SE Labs AAA in Advanced Performance
Cisco Secure Firewall 4225 is the first to get SE Labs AAA for Advanced Performance, proving top speed & protection.
2025. július 24.
Biztonsági szemle
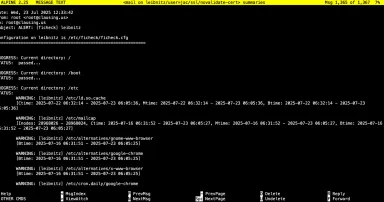
New Tool: ficheck.py, (Thu, Jul 24th)
As I mention every time I teach FOR577, I have been a big fan of file integrity monitoring tools (FIM) since Gene Kim first released Tripwire well over 30 years ago. I've used quite a few of them over the years including tripwire, OSSEC...

2025. július 24.
Biztonsági szemle
ISC Stormcast For Thursday, July 24th, 2025 https://isc.sans.edu/podcastdetail/9540, (Thu, Jul 24th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.

2025. július 24.
Biztonsági szemle
Fixed Ivanti Bugs Still Haunt Japan Orgs 6 Months Later
Chinese threat actors have been feeding off the same Ivanti RCE vulnerabilities we've known about since last year, partly thanks to complications in patching.

2025. július 23.
Biztonsági szemle
Banking Trojan Coyote Abuses Windows UI Automation
It's the first known instance of malware that abuses the UIA framework and has enabled dozens of attacks against banks and crypto exchanges in Brazil.
Oldalszámozás
- Előző oldal ‹‹
- 182. oldal
- Következő oldal ››