Biztonsági szemle

2024. november 5.
Biztonsági szemle
Biden administration prepares second executive order on cybersecurity
Key components of the new order reportedly include pilot programs to advance artificial intelligence-based cyber defense, building on a prior AI-centric executive order signed by President Biden.

2024. november 5.
Biztonsági szemle
Noma debuts AI security platform
After raising $32 million in a Series A funding round, Noma aims to secure the AI development lifecycle from data ingestion to deployment.

2024. november 5.
Biztonsági szemle
NTT Data, Palo Alto Networks partner to enhance AI-driven cybersecurity
NTT Data and Palo Alto Network have entered into a new partnership to deliver a Managed Extended Detection Response Service which uses artificial intelligence to power its advanced threat detection and response capabilities.

2024. november 5.
Biztonsági szemle
Docusign API Abused in Widescale, Novel Invoice Attack
Attackers are exploiting the "Envelopes: create API" of the enormously popular document-signing service to flood corporate inboxes with convincing phishing emails aimed at defrauding organizations. It's an unusual attack vector with a high success...

2024. november 5.
Biztonsági szemle
The Business Case for Customer Identity and Access Management in E-Commerce
This Liminal white paper explores how Customer Identity and Access Management (CIAM) solutions can help your business deliver seamless transactions, increase customer loyalty, and stay compliant—without compromising on security.

2024. november 5.
Biztonsági szemle
Oh, the Humanity! How to Make Humans Part of Cybersecurity Design
Government and industry want to jump-start the conversation around "human-centric cybersecurity" to boost the usability and effectiveness of security products and services.

2024. november 5.
Biztonsági szemle
How to Win at Cyber by Influencing People
Zero trust is a mature approach that will improve your organization's security.
2024. november 5.
Biztonsági szemle
Dark Reading Confidential: Quantum Has Landed, So Now What?
Episode #4: NIST's new post-quantum cryptography standards are here, so what comes next? This episode of Dark Reading Confidential digs the world of quantum computing from a cybersecurity practitioner's point of view -- with guests Matthew McFadden...

2024. november 5.
Biztonsági szemle
On Election Day, Disinformation Worries Security Pros the Most
A Dark Reading poll reveals widespread concern over disinformation about election integrity and voter fraud, even as Russia steps up deepfake attacks meant to sow distrust in the voting process among the electorate.
2024. november 5.
Biztonsági szemle
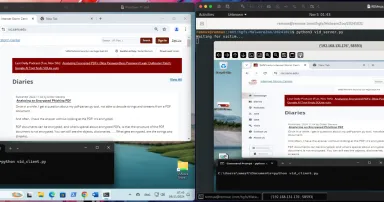
Python RAT with a Nice Screensharing Feature, (Tue, Nov 5th)
While hunting, I found another interesting Python RAT in the wild. This is not brand new because the script was released two years ago[ 1]. The script I found is based on the same tool and still has a low VT...

2024. november 5.
Biztonsági szemle
Iranian APT Group Targets IP Cameras, Extends Attacks Beyond Israel
The Iran-linked group Emennet Pasargad aims to undermine public confidence in Israeli and Western nations by using hack-and-leak campaigns and disrupting government services, including elections.

2024. november 5.
Biztonsági szemle
ISC Stormcast For Tuesday, November 5th, 2024 https://isc.sans.edu/podcastdetail/9208, (Tue, Nov 5th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
Oldalszámozás
- Előző oldal ‹‹
- 583. oldal
- Következő oldal ››